Calyx Public Jabber/XMPP Server
Calyx Public Jabber/XMPP Server
The Calyx Institute operates an experimental free public conferencing server that provides chat service using jabber, also known as XMPP.

The Calyx Institute operates an experimental free public conferencing server. The server provides chat service using jabber, ( also known as XMPP) the open-standards protocol for instant messages and voice communication. The server is reachable at the address jabber.calyxinstitute.org. It is also reachable via a Tor hidden service (see below for details).
The server allows in-band registration so you can create an account from within a standard client such as Pidgin or Adium or ChatSecure on Android or Apple iOS.
If you have any complaints about abusive behavior from any accounts on the server please email abuse@calyxinstitute.org with full details
Data retention policies
The server does not create any records of who you communicate with.
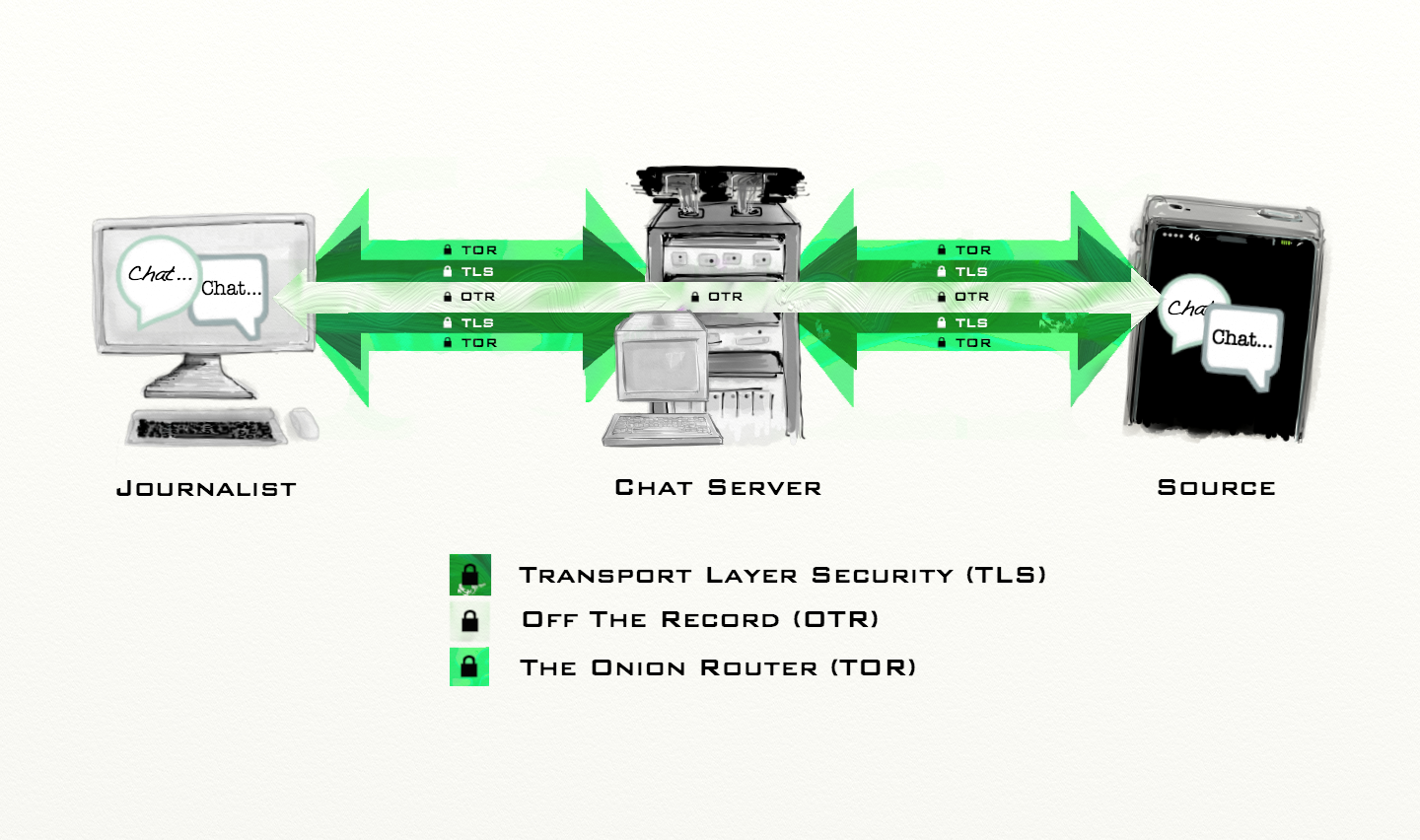
It does not log the content of any communications ( and in fact since the server forces you to use Off-The-Record Messaging, we can never get access to the plain text of your communications ) For more information about what Off-The-Record is and why we require it, as well as links to XMPP clients that support OTR, see this page.
If you choose to access the server via its Tor hidden service then we know virtually nothing about you. We can't know what ISP you use, or even what country you live in.
The use of this server is governed by The Calyx Institute's privacy policy.
A few notes about the security of the server (and its associated records)
 Our intention is to take security on this server to the highest possible level we can achieve. In pursuit of that goal, we have taken the following precautions:
Our intention is to take security on this server to the highest possible level we can achieve. In pursuit of that goal, we have taken the following precautions:
StartTLS / SSL encryption is required for all client connections. The server is configured to prefer ephemeral ( Forward Secrecy ) encryption ciphers, but will fall back to AES256-SHA or AES128-GCM-SHA256 if servers or clients don't support the ephemeral flavors.
Our RSA key size is 4096 bits. In recent years, various security organizations have recommended that RSA key sizes less than 2048 bits be discontinued. In particular the United States National Institute of Standards and Technology (NIST) recommends using 2048 bit RSA keys until 2030 at which time it predicts they will not be considered strong enough any longer. But really, why wait until 2030 ? We have chosen to skip 2048 bits and have adopted a 4096 bit key size now.
Tor Hidden Service - So that users can access the server more anonymously, it is also available as a Tor hidden service at the address: ijeeynrc6x2uy5ob.onion If you use XMPP through the .onion address then that makes it much more difficult for observers to know ( through metadata collection or passive observation ) who is connecting to the server. At the moment the only client that we know of that has built-in ability is ChatSecure on Android. It should be possible with just about any client however to direct it to use a tor socks proxy.
The calyxinstitute.org DNS zone is signed with DNSSEC You can check the status of the chain of trust using the dnsviz tool operated by Sandia National Laboratories.
We have published DANE/TLSA dns records containing the fingerprint of the SSL certificate used on the server. We are unsure if any XMPP clients actually check the DANE/TLSA records however. Hopefully we will find out more soon.
You can verify the above security policies using XMPP.net's IM observatory
The server now forces the use of Off The Record Messaging to further encrypt your private conversations end-to-end. We have already written a guide to using OTR on Mac OS X with Adium. We intend to write similar documents for Windows / Pidgin and other combinations. If you would like to help with this type of writing then please get in touch.
If you use OTR + SSL + Tor then you will have taken perhaps the most conservative steps presently available to the general public to ensure the security of your instant messaging.
The fingerprints/hashes of our TLS certificate are as follows:
jabber.calyxinstitute.org: SHA256 04 26 6C 9D 65 B4 92 46 24 27 53 D2 EC 51 5F 69 A2 B0 4F 89 EE 90 66 0D 3A 9A 24 C2 9E DA B5 D6 DNSName *.calyxinstitute.org or calyxinstitute.org